For many, encryption is a golden standard in data protection and the best way to ensure a high level of security in professional backup solutions. Could encryption be used as a mitigation mechanism against data breach events too? Yes. AES encryption is truly one of the most effective tools in the security professional’s arsenal. In this article, we will touch upon a variety of fundamental topics in data encryption. And if you prefer a more practical approach there is also an in-depth presentation of how Xopero ONE allows to encrypt [and protect] backed up data.
What is AES encryption?
Nowadays, the Advanced Encryption Standard also known as AES has become one of the most popular block encryption algorithms. And there is a very good reason why it happened.
AES includes three block ciphers: AES 128 which uses a 128-bit key length to encrypt and decrypt data blocks. AES 192 with a 192-bit key length. There is also AES 256 which uses a 256-bit key length. Each cipher encrypts and decrypts data in blocks of 128 bits using cryptographic keys of 128, 192 and 256 bits, respectively. How does encryption work?
Let’s start by explaining the round term. A round is a function used in the rounds during the encryption and decryption process. Every round consists of several steps – substitution, transposition, and mixing of the input data, during which it is transformed into the final fully ciphered output. There are 10 rounds for 128-bit keys, 12 rounds for 192-bit keys, and 14 rounds for 256-bit keys.
Cracking the AES-generated cipher, even with one of the most powerful computers available on the planet, would take about 10^18 years. That’s a lot! There is no surprise then, that since the development of the AES algorithm, it remains unbreakable.
Why should you encrypt your backup?
You are probably aware that your company’s data is crucial for your business’s success, and having proper protection in place is very important. There are many factors you need to take into consideration.
Imagine that somehow, your storage device, where you keep all the data, gets stolen. If you keep your data there encrypted, especially with the 258 AES CBC encryption that Xopero provides, you can rest assured that no one will be able to access your data and steal any of your company secrets.
This also applies to possible data theft. How exactly? By stopping a security breach from escalating into a data breach. Even if bad actors gain access to your company’s infrastructure, data encrypted with AES 265 will be simply unusable to them.
Data encryption in Xopero ONE
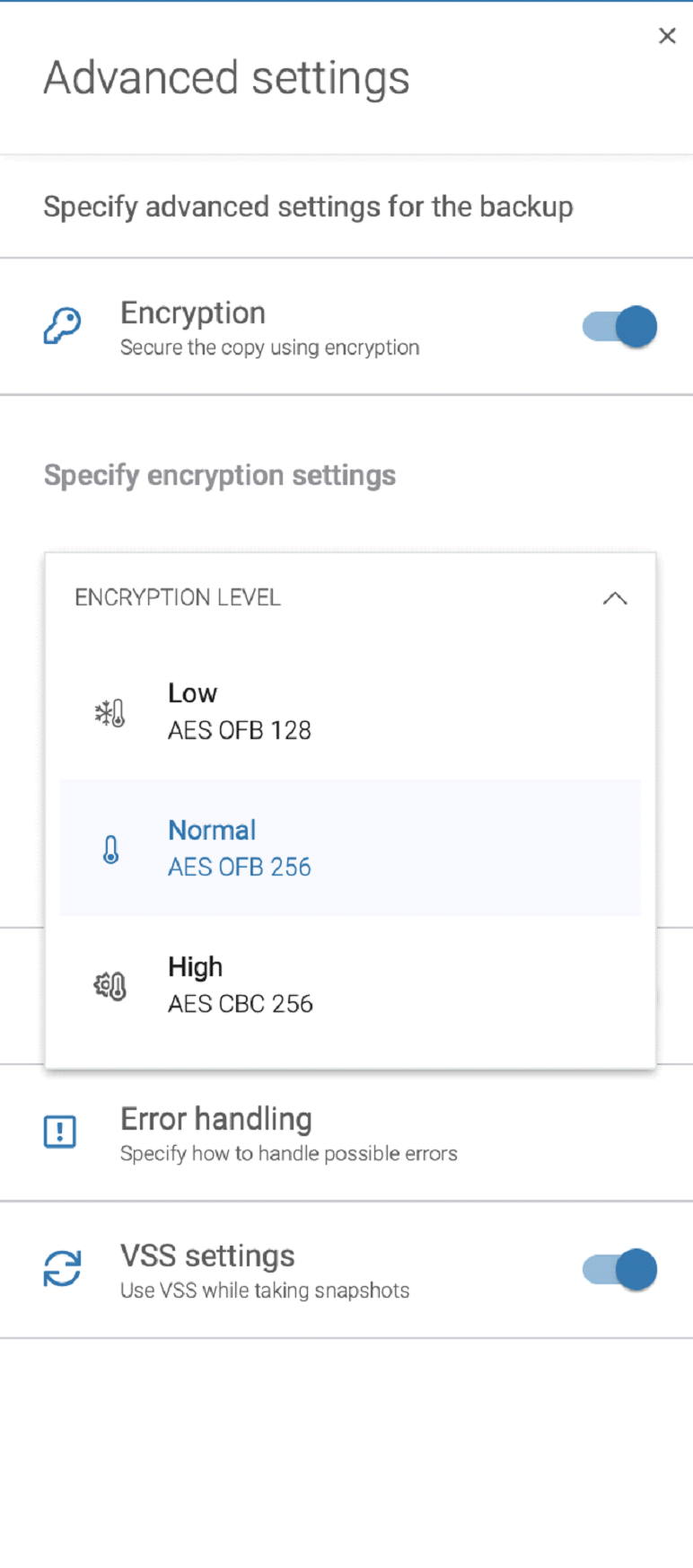
Xopero ONE provides three levels of encryption:
- Low – encrypted with AES working in OFB mode with a key length of 128 bits.
- Normal – encrypted with AES working in OFB mode with a key length of 256 bits.
- High – encrypted with AES working in CBC mode with a key length of 256 bits.
There is also an option to disable encryption entirely, but we strongly recommend against it.
Encryption settings can be found in Backup plan > New plan > Advanced settings > Encryption.
The chosen encryption level influences the time it takes to perform a backup but is also responsible for the security of your backed up data.
When it comes to the encryption key, users can choose to set one themselves or generate it in a fully automatic way. A key saved in the form of a string is then stored in the secure Password Manager. In the same way, users can also store their passwords. A little warning, without the right key, data decrypting will not be possible, hence the Manager is truly a neat feature.
Summary
Whether you choose to encrypt your data or not, Xopero offers many solutions to keep your business data secure:
- Protect your Microsoft 365 data in minutes – add your organization, choose users and data to protect, storage (on-premise or cloud) and submit it to a predefined or customized backup plan.
- Cross-user recovery – Restore protected data to the original user destination or choose a different one from your Microsoft 365 suite
- Central, user-friendly management #1 – simple, the most intuitive central management web console. Thanks to the most user-friendly interface, setting up efficient backup and recovering data are the simplest ever.
- Unlimited retention – Store your data as long as you need and take advantage of multiple backup rotation schemes – FIFO, Grandfather-Father-Son, Forever Incremental – choose yours.
- Granular recovery – fast, and point-in-time recovery of all or only selected types of data – folders, mailboxes, documents, or even particular emails.
- and much more… You can try for free all the available features here.