Welcome to the next episode of the Xopero Security Center! Autodesk 3ds Max – a very popular software used by architects has a serious flaw. Recently, it was exploited by an advanced hackers-for-hire group. The attack hit an architecture company involved in luxury real-estate projects worth billions of dollars. What more?
Attackers use Unicode and HTML to help malicious phishing emails slip past detection tools
Cybercriminals have been spotted using HTML/CSS and Unicode tricks to bypass tools meant to block malicious emails.
It definitely looks like we are dealing with new phishing techniques. Some attackers rely on hidden text and zero-font attacks. They put invisible characters between the letters of an email. It doesn’t trigger email defenses with phrases like “password expired” or “Office 365.” While others…
…attackers use their knowledge of HTML/CSS and Unicode to disguise phishing emails in a very smart way. One of the new techniques involves Unicode’s “soft hyphen,” also known as “syllable hyphen”. In typesetting, this is used to tell the renderer where to safely break a line and insert a visible hyphen. The soft hyphen normally renders as invisible. If we scan the malicious email for phrases like “change your password,” there will be no results. Why? Because the attacker had written such phrases as “c-h-a-n-g-e- -y-o-u-r- -p-a-s-s-w-o-r-d-.” To a user, they appear as normal. Scanners aren’t configured to look for this type of content, so they may not raise any flags.
Another great example. When the attacker typed “Office 365,” they used the HTML <font> to make it look like a logotype. People often register the text in phishing mails as a logo.
Attackers also used the “display:none” setting, an element of CSS that tells a browser to render text as invisible. The phisher made the error of putting text they wanted the user to see within a span element, even though the CSS was written to render spans as hidden. Then the attacker used the invisible span trick to hide repeating text “40008” between words of the phrase “Password for user[@]example[.]com. The “40008” text could be another tactic to bypass the pattern-matching in security tools. If there is a random number generated for every email, there’s less of a chance tools will associate them with the same phishing kit.
Security problem. Defending users against the soft hyphen technique may be challenging.
It’s in the attacker’s interest to use several unique Unicode characters. On the other hand the more Unicode characters a company adds to its security tool, the slower it will be… and it may not necessarily scale well.
Hackers compromised an unnamed architecture firm via Autodesk 3ds Max exploit
An advanced hackers-for-hire group has compromised computers of an architecture firm involved in luxury real-estate projects worth billions of US dollars. The victim is a recognized company working with luxury real-estate developers in the U.S., the U.K., Australia, and Oman. How? Architects are using Autodesk 3ds Max…
Earlier this month, Autodesk warned that an exploit for the Autodesk 3ds Max – specifically MAXScript scripting utility exists in the form of a malicious plugin called “PhysXPluginMfx.” When loaded in Autodesk 3ds Max, the plugin can infect other MAX files, thus spreading to other users on the network.
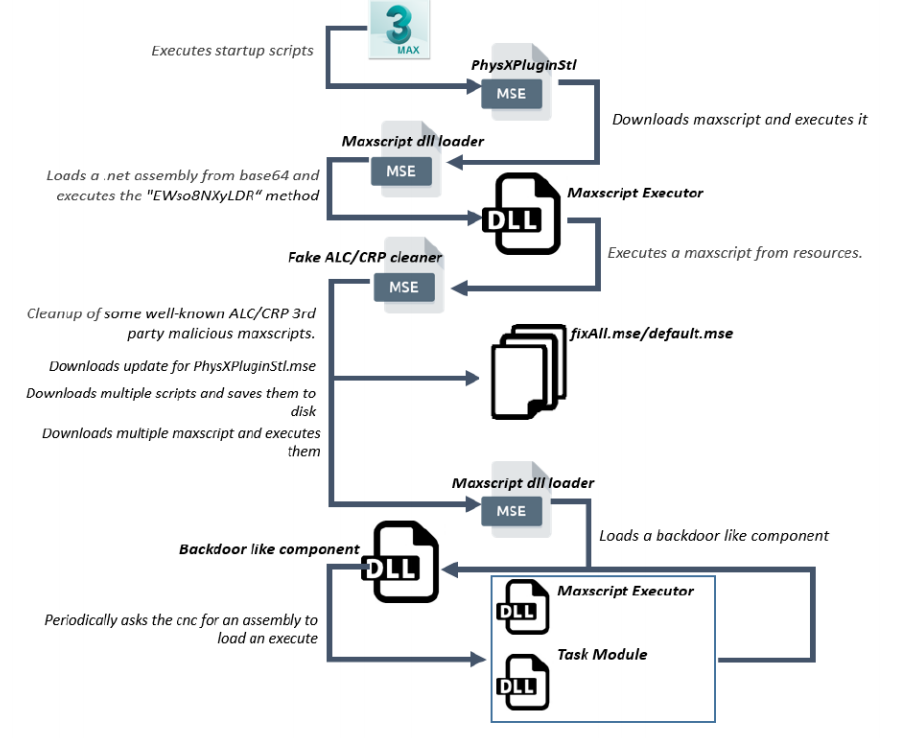
The way that the attack has been carried on shows that the cybercriminals had prior knowledge of the company’s security systems and used software applications. Hackers were carefully planning the attack to infiltrate the company and exfiltrate data undetected.
The malware used during this attack collected details about the compromised host. Such as computer name, username, extracted passwords, and history data from Google Chrome. Malware also has been stealing files with specific extensions.
To remain undetected, hackers used an interesting trick. It made the malicious binary sit dormant if Task Manager or Performance Monitor were running. Depending on how much window area was visible for these two applications, a flag was set to instruct the malware to sleep. Thus reducing CPU usage and placing it lower in the list of power-hungry processes. They also employed compression only for some files. Data that would attract unnecessary attention if archived, have been skipped.
After a decade, Qbot Trojan malware gains new, dangerous tricks
The Qbot Trojan (also known as Qakbot or Pinkslipbot) has been plaguing users and businesses for over a decade (!) Still coming up with new tricks that make it one of the most prevalent and successful malware threats. It is estimated to have claimed at least 100,000 victims across the world.
Cybersecurity researchers from Check Point published research on the new trend. According to this, Outlook users are susceptible to a module designed to collect and compromise email threads on infected machines.
A new variant of QBot is being deployed as a malicious payload by operators of the Emotet Trojan. The researchers estimate that one particularly extensive campaign in July impacted roughly 5% of organizations worldwide.
The malware lands on a vulnerable machine via phishing documents containing URLs to .ZIP files that serve VBS content, calling the payload from one of six hardcoded encrypted URLs.
Once a PC has been infected, a new and interesting module in the modern QBot variant described as an “email collector module” extracts all email threads and uploads them to the attacker’s C2 server.
The hijacked threads are then used to propagate the malware further. By jumping on legitimate threads, unwitting readers might think messages sent by the attackers are legitimate… And therefore, are more likely to click on infected attachments.
Subjects tracked by the team include tax payment reminders, job recruitment content, and COVID-19-related messages.
QBot is able to steal browsing data, email records, and banking credentials. One of the Trojan’s modules downloads Mimikatz to harvest passwords. It is also able to perform browser web injections and install malicious payloads including ransomware ProLock. Besides, QBot connects infected machines as slave nodes in a wider botnet.
SunCrypt Ransomware sheds light on the Maze ransomware cartel
In June, we unveiled that the Maze threat actors created a cartel of ransomware operations. The main aim was to share information and techniques to help each other extort their victims.
When first started, this cartel included Maze and LockBit, but soon expanded to include Ragnar Locker. Now, SunCrypt Ransomware joins this big criminal team.
This ransomware family began operating in October 2019, but was not very active. It may change – now as SunCrypt operators say they have “two-way communication channels”.
How does the cartel work and earn? It is still pretty mysterious but sharing revenue from the successful operation sounds very promising as more and more operators want to have a slice of the cake. Based on SunCrypt operators’ statement they were brought in because… Maze can’t handle all of the potential attacks. So they provide compromised network access to cartel members in exchange for a revenue share.
For months, Maze has been hosting a data leak site and launching attacks from known public IP addresses. Yet in all this time, their services remain intact and have not been taken down by law enforcement.
The SunCrypt ransomware in short. The ransomware is currently being distributed as a DLL that, when executed, will encrypt a computer’s files. Then it will append a hexadecimal hash to the end of each file name. It is not known what this hash represents.
In every folder, a ransom note named YOUR_FILES_ARE_ENCRYPTED.HTML is created. It contains information on what happened to a victim’s files and a link to the Tor payment site. The Tor link enclosed in a ransom note is hardcoded into the ransomware executable. This means that every victim encrypted by a particular SunCrypt executable will have the same Tor payment site link.
The Tor payment site does not have automated features. It simply contains a chat screen where a victim can negotiate a ransom with the SunCrypt threat actors. Furthermore, every ransom note contains a link to the SunCrypt data leak site that the threat actors warn will be used to publish the victim’s data.
SunCrypt is currently being analyzed for weaknesses. It is not known if it is possible to recover files for free.
Please be advised that the best protection against ransomware and its effects is to invest in proven antivirus solutions and backup and disaster recovery software.
Do you have thirst for knowledge? There is ten more cybersecurity stories below
1. New AI algorithm to detect cryptocurrency miners as they steal power (HelpNetSecurity)
2. Phishing Attack Used Box to Land in Victim Inboxes (Dark Reading)
3. Cisco Patches ‘High-Severity’ Bugs Impacting Switches, Fibre Storage (Threat Post)
4. A quarter of the Alexa Top 10K websites are using browser fingerprinting scripts (ZDNet)
5. From zero to hero: Zero2Automated malware reverse engineering course (Bleeping Computer)
6. New Zealand stock exchange halted trading after DDoS attacks (Bleeping Computer)
7. Giveaway Scam Infects 65,000 Devices with Malware (Infosecurity Magazine)
8. Lemon_Duck cryptominer malware now targets Linux devices (Bleeping Computer)
9. 350 million decrypted email addresses left exposed on an unsecured server (Security Affairs)
10. UltraRank hackers steal credit cards from hundreds of stores (Bleeping Computer)